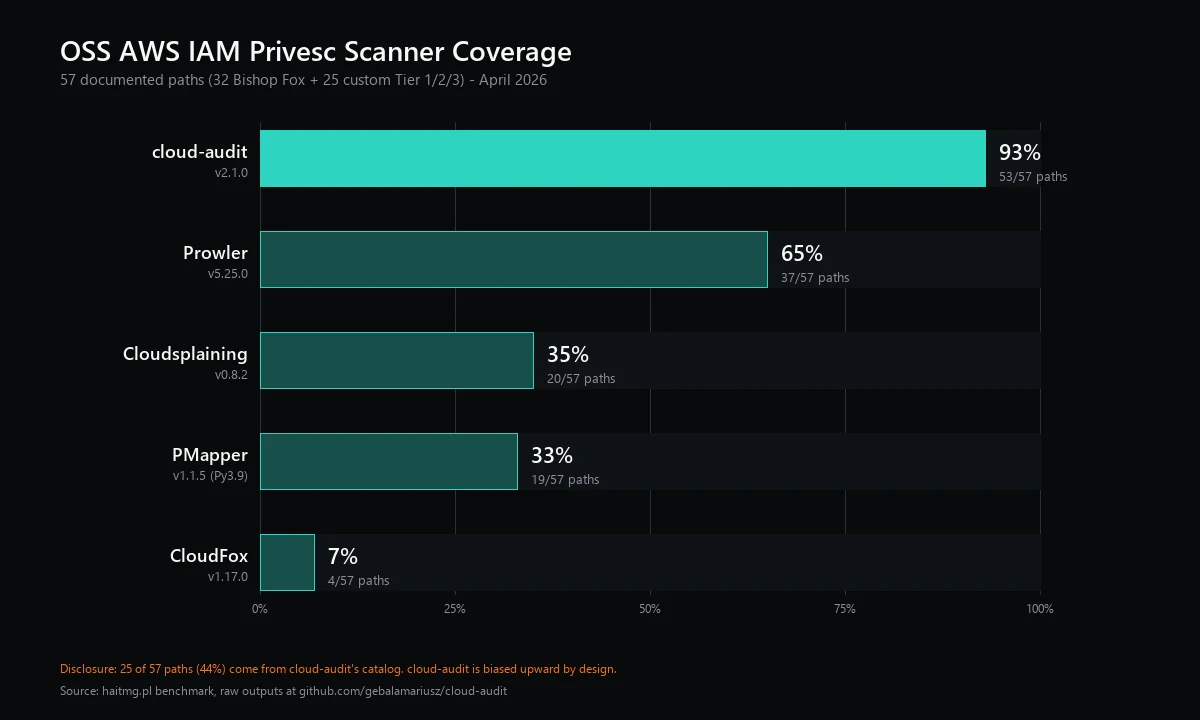
5 AWS IAM Privesc Scanners vs 57 Paths: Coverage from 7% to 93%
Disclosure: I am the author of cloud-audit. 25 of the 57 paths in this benchmark (44%) come from cloud-audit’s v2.1.0 catalog, so the matrix has structural bias toward cloud-audit. On the bias-free Bishop Fox subset of 32 paths, Prowler ranks first (31/32, 97%) and cloud-audit second (28/32, 88%). I have flagged every place this matters in the analysis below.
Bottom line (April 2026): Across 57 documented AWS IAM privilege escalation paths, cloud-audit detected 53 (93%), Prowler 37 (65%), Cloudsplaining 20 (35%), PMapper 19 (33%), and CloudFox 4 (7%). No single tool covers everything - the only combination that hits 57/57 on this bench is cloud-audit + Prowler + PMapper (or CloudFox). The full coverage matrix, per-tool design tradeoffs, and seven caveats about how to read these numbers are below.
On December 17, 2025, Datadog Security Labs published pathfinding.cloud. The conclusion was, to put it mildly, disheartening - 27 of the 65 documented AWS IAM privilege escalation paths (42%) were not detected by any open source tool evaluated. The article itself is very comprehensive, but one thing was missing: a published tool-by-tool matrix. Hence the idea for this post. I set up a clean test environment containing 57 escalation paths and ran five OSS scanners against it. This post describes what each scanner detected.
TL;DR
| Tool | Version | Paths Detected | Coverage | Scan Time | Best for |
|---|---|---|---|---|---|
| cloud-audit | 2.1.0 | 53/57 | 93% | 24s | Privesc + 2024-2026 patterns |
| Prowler | 5.25.0 | 37/57 | 65% | 4m 29s | Compliance breadth (572 checks) |
| Cloudsplaining | 0.8.2 | 20/57 | 35% | 20s | Policy hygiene, 5 categories |
| PMapper | 1.1.5 (Python 3.9 only) | 19/57 | 33% | 1m 59s | AssumeRole chain graphs |
| CloudFox | 1.17.0 | 4/57 | 7% | 1m 51s | Offensive recon, not privesc |
Bias-free subset (Bishop Fox iam-vulnerable, 32 paths only): Prowler 31/32 (97%), cloud-audit 28/32 (88%), Cloudsplaining 20/32 (63%), PMapper 14/32 (44%), CloudFox 1/32 (3%). On the 32 paths that did not originate in cloud-audit’s catalog, Prowler is the leader. The 25 custom Tier 1/2/3 paths are where the matrix stops being neutral.
The numbers above only demonstrate the effectiveness of privilege escalation detection. Each tool has a different primary purpose, and treating them as a single category would be a mistake - especially considering that 44% of these paths come from cloud-audit’s catalog. A detailed analysis follows.
Why this benchmark exists
Datadog Security Labs published pathfinding.cloud. This community-maintained library documents 65 AWS IAM privilege escalation paths. To quote a powerful statement straight from the article:
Of the 65 paths currently in the pathfinding.cloud library, 27 of them, or 42%, are not detected by any of the open-source tools we evaluated.
This number is often repeated in other articles on this topic. However, it doesn’t explicitly specify which specific tool detected each path. I think anyone considering reviewing their AWS account for this type of vulnerability needs such a comparison.
I love personally confirming research that appears on reputable portals. First, it’s a great path for self-development, and second, I conduct cloud audits myself and wanted to know how the theory compares to the practice. The table below presents the results.
Test bench
The bench has 57 paths, deployed to a fresh AWS account in eu-central-1:
32 paths from Bishop Fox iam-vulnerable:
To deliberately create a vulnerability in an AWS account that is completely clean of other resources, I used a Terraform module that intentionally misconfigures IAM resources (tailored specifically for such tests). It includes 21 classic Rhino Security Labs paths from 2018, as well as newer additions (CodeBuild, SageMaker variants, SSM:SendCommand, SSM:StartSession, EC2 Instance Connect, CloudFormation:UpdateStack, and a 3-hop AssumeRole chain).
25 custom paths covering Tier 1/2/3 patterns from cloud-audit v2.1.0:
These are the cloud-audit paths added in its current development release. They map to documented attack vectors:
| Tier | Pattern | Example | Real-world reference |
|---|---|---|---|
| 1 | Resource Policy Abuse | lambda:AddPermission | HackingTheCloud Lambda resource policy abuse |
| 1 | EC2 Instance Profile hijack | ec2:AssociateIamInstanceProfile + iam:PassRole | Praetorian: Pivoting Cloud Workloads |
| 1 | Deny-removal | iam:DeleteRolePolicy + sts:AssumeRole | Pacu module documentation |
| 1 | MFA bypass | iam:DeactivateMFADevice | AWS IAM hardening guides |
| 2 | New compute primitives | bedrock:CreateAgent + iam:PassRole | SoftwareSecured AI vectors |
| 2 | SSM compute hijack | ssm:SendCommand, ssm:StartSession, ssm:GetParameter | Rich Infante: SSM in EC2 privesc |
| 2 | Compute Hijack (no PassRole) | codebuild:UpdateProject, apprunner:UpdateService | HackTricks Cloud SSM Privesc |
| 3 | Lateral AssumeRole Direct | Alice has sts:AssumeRole, AdminRole trusts Alice | Standard IAM trust pattern |
| 3 | Lateral AssumeRole Chain | Bob -> JumpRole -> AdminEnd | Elastic STS Role Chaining detection |
| 3 | WildcardTrust | Role with Principal: { AWS: "*" } | HackingTheCloud wildcard principal |
| 3 | CrossAccountRoot | Role trusts external account :root | AWS Security Bulletin AWS-2025-031 (CVE-2025-14503) |
The 25 custom paths come from cloud-audit’s catalog but are documented attack vectors. I will return to the bias question later.
CVE-2025-14503 (December 2025) maps to two paths in this bench. AWS Security Bulletin AWS-2025-031 documented Harmonix on AWS EKS shipping with a wildcard trust policy (
Principal: { AWS: "*" }), allowing any AWS account to assume the role. CT-24 (WildcardTrust) and CT-25 (CrossAccountRoot) in the matrix below are this exact CVE class. Detection results: cloud-audit, Prowler, and CloudFox catch both. PMapper catches WildcardTrust only (misses CrossAccountRoot). Cloudsplaining misses both - this category is outside its policy-hygiene scope.
Tools tested
Each tool occupies a different niche. The matrix only measures privilege escalation. Read it that way. For a broader survey of what’s worth installing in 2026 (including Trivy and Heimdall, which I left out of this matrix), see 5 Open-Source AWS Security CLI Tools Worth Trying in 2026.
Prowler 5.25.0 - 572 checks across multiple compliance frameworks (CIS, SOC2, HIPAA, NIST, ISO, PCI), MITRE ATT&CK mapping, GuardDuty integration. Six checks specifically address privilege escalation: iam_policy_allows_privilege_escalation, iam_inline_policy_allows_privilege_escalation, iam_no_custom_policy_permissive_role_assumption, iam_role_cross_service_confused_deputy_prevention, plus two for inline/customer admin policies. Privesc is one dimension among many. For a feature-by-feature comparison against ScoutSuite and cloud-audit, see Prowler vs ScoutSuite vs cloud-audit: 572 Checks vs 94.
Cloudsplaining 0.8.2 - From Salesforce, BSD-3 licensed. Five categories: PrivilegeEscalation, DataExfiltration, ResourceExposure, CredentialsExposure, InfrastructureModification. The privesc category covers 22 methods that map to the original 2018 Rhino Security Labs research. Last release October 2025, actively maintained.
PMapper 1.1.5 - From NCC Group. Builds a directed graph of IAM principals and edges (assume-role, service-role, etc.). Last release January 2022 - over four years old. Issues #130, #131, and #140 on its GitHub flag broken Python 3.10+ support due to collections.abc import changes. Unresolved for the entire stretch. It still works in a Python 3.9 venv. To run it on a modern system you install Python 3.9 alongside your default Python and create a dedicated venv just for PMapper.
CloudFox 1.17.0 - From Bishop Fox. Offensive reconnaissance tool with 30+ commands focused on Lambda enumeration, secret discovery, EC2 mapping, role-trust analysis, and similar. Has a pmapper subcommand that promises privesc analysis but requires existing PMapper graph data. CloudFox is not a privesc detector and including it here is a category mismatch - I included it because it gets recommended in the same conversations as the others.
cloud-audit 2.1.0 - The tool I maintain. Two-stage detection: action-based (60 methods in a curated catalog) and lateral movement (graph BFS through trust policies). Specialized for privilege escalation; weaker than Prowler on compliance, weaker than Cloudsplaining on data exfiltration, weaker than CloudFox on offensive recon.
The matrix
How to read this table: Y = detected, N = missed. Path IDs: BF-N comes from the Bishop Fox iam-vulnerable Terraform module, CT-N comes from custom Tier 1/2/3 additions in cloud-audit’s catalog. Wide tables scroll horizontally on mobile.
| Path ID | Resource | Method | Category | cloud-audit | Prowler | Cloudsplaining | PMapper | CloudFox |
|---|---|---|---|---|---|---|---|---|
| BF-1 | privesc1 | iam:CreatePolicyVersion | IAM Self-Mutation | Y | Y | Y | Y | N |
| BF-2 | privesc2 | iam:SetDefaultPolicyVersion | IAM Self-Mutation | Y | Y | Y | Y | N |
| BF-3 | privesc3 | EC2 RunInstances + InstanceProfile | PassRole+Service | Y | Y | Y | Y | N |
| BF-4 | privesc4 | iam:CreateAccessKey | Credential Access | Y | Y | Y | N | N |
| BF-5 | privesc5 | iam:CreateLoginProfile | Credential Access | Y | Y | Y | N | N |
| BF-6 | privesc6 | iam:UpdateLoginProfile | Credential Access | Y | Y | Y | N | N |
| BF-7 | privesc7 | iam:AttachUserPolicy | IAM Self-Mutation | Y | Y | Y | N | N |
| BF-8 | privesc8 | iam:AttachGroupPolicy | IAM Self-Mutation | Y | Y | Y | N | N |
| BF-9 | privesc9 | iam:AttachRolePolicy | IAM Self-Mutation | N | Y | N | N | N |
| BF-10 | privesc10 | iam:PutUserPolicy | IAM Self-Mutation | Y | Y | Y | N | N |
| BF-11 | privesc11 | iam:PutGroupPolicy | IAM Self-Mutation | Y | Y | Y | N | N |
| BF-12 | privesc12 | iam:PutRolePolicy | IAM Self-Mutation | N | Y | N | N | N |
| BF-13 | privesc13 | iam:AddUserToGroup | Credential Access | Y | Y | Y | N | N |
| BF-14 | privesc14 | iam:UpdateAssumeRolePolicy | Trust Policy Abuse | Y | Y | Y | Y | N |
| BF-15 | privesc15 | PassRole+Lambda+Invoke | PassRole+Service | Y | Y | Y | Y | N |
| BF-16 | privesc16 | PassRole+Lambda+EventSource | PassRole+Service | Y | Y | Y | Y | N |
| BF-17 | privesc17 | lambda:UpdateFunctionCode | Lambda Code Mod | Y | Y | Y | N | N |
| BF-18 | privesc18 | PassRole+Glue:CreateDevEndpoint | PassRole+Service | Y | Y | Y | N | N |
| BF-19 | privesc19 | Glue:UpdateDevEndpoint | Compute Hijack | Y | Y | Y | N | N |
| BF-20 | privesc20 | PassRole+CloudFormation:CreateStack | PassRole+Service | Y | Y | Y | Y | N |
| BF-21 | privesc21 | PassRole+DataPipeline | PassRole+Service | Y | Y | Y | N | N |
| BF-22 | privesc-AssumeRole | 3-hop AssumeRole chain | Lateral AssumeRole | N | N | N | Y | Y |
| BF-23 | privesc-codeBuild | PassRole+CodeBuild | PassRole+Service | Y | Y | N | Y | N |
| BF-24 | privesc-CFNUpdate | PassRole+CFN:UpdateStack | PassRole+Service | N | Y | N | N | N |
| BF-25 | privesc-ec2InstanceConnect | EC2InstanceConnect:SendSSHPublicKey | Compute Hijack | Y | Y | N | N | N |
| BF-26 | privesc-sageNotebook | PassRole+SageMaker:Notebook | PassRole+Service | Y | Y | N | Y | N |
| BF-27 | privesc-sagePresignedURL | SageMaker:CreatePresignedNotebookUrl | Compute Hijack | Y | Y | N | N | N |
| BF-28 | privesc-sageProcessingJob | PassRole+SageMaker:ProcessingJob | PassRole+Service | Y | Y | N | Y | N |
| BF-29 | privesc-sageTrainingJob | PassRole+SageMaker:TrainingJob | PassRole+Service | Y | Y | N | Y | N |
| BF-30 | privesc-ssmSendCommand | SSM:SendCommand | Compute Hijack | Y | Y | N | Y | N |
| BF-31 | privesc-ssmStartSession | SSM:StartSession | Compute Hijack | Y | Y | N | Y | N |
| BF-32 | privesc-sre | Group admin policy | Credential Access | Y | Y | Y | N | N |
| CT-1 | custom-lambda-addperm | Lambda:AddPermission | Resource Policy Abuse | Y | Y | N | N | N |
| CT-2 | custom-lambda-layer | Lambda:AddLayerVersionPermission | Resource Policy Abuse | Y | N | N | N | N |
| CT-3 | custom-ec2-associate | PassRole+EC2:AssociateInstanceProfile | PassRole+Service | Y | N | N | N | N |
| CT-4 | custom-ec2-replace | PassRole+EC2:ReplaceInstanceProfileAssociation | PassRole+Service | Y | N | N | N | N |
| CT-5 | custom-ip-swap | InstanceProfileRoleSwap | PassRole+Service | Y | N | N | N | N |
| CT-6 | custom-ecs-update-service | PassRole+ECS:UpdateService | PassRole+Service | Y | N | N | N | N |
| CT-7 | custom-ecs-register | PassRole+ECS:RegisterTaskDefinition | PassRole+Service | Y | N | N | N | N |
| CT-8 | custom-delete-rolepolicy | DeleteRolePolicy + AssumeRole | IAM Self-Mutation | Y | N | N | Y | N |
| CT-9 | custom-delete-userpolicy | DeleteUserPolicy | IAM Self-Mutation | Y | N | N | N | N |
| CT-10 | custom-detach-rolepolicy | DetachRolePolicy + AssumeRole | IAM Self-Mutation | Y | N | N | Y | N |
| CT-11 | custom-detach-userpolicy | DetachUserPolicy | IAM Self-Mutation | Y | N | N | N | N |
| CT-12 | custom-csr | CreateServiceLinkedRole | IAM Self-Mutation | Y | N | N | N | N |
| CT-13 | custom-deactivate-mfa | DeactivateMFADevice | Credential Access | Y | N | N | N | N |
| CT-14 | custom-delete-mfa | DeleteVirtualMFADevice | Credential Access | Y | N | N | N | N |
| CT-15 | custom-update-accesskey | UpdateAccessKey | Credential Access | Y | N | N | N | N |
| CT-16 | custom-apprunner-create | PassRole+AppRunner:CreateService | PassRole+Service | Y | Y | N | N | N |
| CT-17 | custom-bedrock-agent | PassRole+Bedrock:CreateAgent | PassRole+Service | Y | N | N | N | N |
| CT-18 | custom-stepfunctions | PassRole+StepFunctions:CreateStateMachine | PassRole+Service | Y | N | N | N | N |
| CT-19 | custom-codebuild-hijack | CodeBuild:UpdateProject | Compute Hijack | Y | Y | N | N | N |
| CT-20 | custom-apprunner-hijack | AppRunner:UpdateService | Compute Hijack | Y | Y | N | N | N |
| CT-21 | custom-ssm-getparameter | SSM:GetParameter | Credential Access | Y | N | N | N | N |
| CT-22 | custom-lateral-alice | AssumeRole:Direct | Lateral AssumeRole | Y | N | N | Y | Y |
| CT-23 | custom-lateral-bob | AssumeRole:Chain (2-hop) | Lateral AssumeRole | Y | N | N | Y | N |
| CT-24 | custom-lateral-WildcardRole | AssumeRole:WildcardTrust | Lateral AssumeRole | Y | Y | N | Y | Y |
| CT-25 | custom-lateral-CrossAcctRole | AssumeRole:CrossAccountRoot | Lateral AssumeRole | Y | Y | N | N | Y |
Per-tool analysis
cloud-audit (53/57)
Detected all 25 custom Tier 1/2/3 paths and 28 of 32 Bishop Fox paths.
The four misses are conscious design decisions, not catalog gaps:
-
BF-9 (AttachRolePolicy) and BF-12 (PutRolePolicy): cloud-audit requires
iam:AttachRolePolicypaired withsts:AssumeRole(you must be able to assume the role you just modified). Bishop Fox’s setup gives only the IAM action without the assume-role permission. Whether this should fire is a judgment call - some auditors prefer to flag the action regardless and force a manual review; others prefer to suppress paths that cannot actually be exploited. cloud-audit takes the latter position. -
BF-22 (3-hop AssumeRole chain) and BF-24 (PassRole+CFN:UpdateStack): Both start from a sandbox admin user with
AdministratorAccessattached. cloud-audit’s lateral detector skips already-admin principals (no need to escalate from admin). PMapper detects the chain because it does not skip admins for this kind of analysis. Again - judgment call. Skipping admins keeps the report quiet; not skipping them surfaces patterns auditors might want to know about anyway.
These four are not bugs. They are positions on a tradeoff. Document either choice clearly and move on.
Bias caveat: 25 of 57 paths come from cloud-audit’s v2.1.0 catalog. cloud-audit was explicitly designed to detect them. The right way to read this is: “for the patterns cloud-audit’s author considered relevant in 2026, the tool detects them.” That is what authoring a catalog gives you.
Prowler (37/57)
Detected via iam_policy_allows_privilege_escalation and iam_inline_policy_allows_privilege_escalation - two checks that internally cover roughly the same 22 patterns Cloudsplaining covers. Plus standalone checks for permissive role assumption and confused deputy. Picked up four of the 25 custom paths through the privesc check (Lambda:AddPermission, AppRunner CreateService, CodeBuild UpdateProject, AppRunner UpdateService) plus WildcardTrust and CrossAccountRoot via separate trust-policy checks.
Strengths beyond this matrix: Prowler is a different category of tool. 572 checks, 30+ AWS services, multi-framework compliance evidence (CIS, SOC2, HIPAA, NIST, ISO, PCI). Privilege escalation is a footnote in its scope. If you are running a single tool for compliance evidence and broad AWS hygiene, Prowler is the natural pick - its privesc gap is acceptable because that is not what it sells itself as.
Limitation: Prowler reports policies, not principals. The output is “policy X enables escalation” rather than “user Y can escalate via Z.” Mapping policy violations back to specific principals is left to the reader.
Cloudsplaining (20/57)
Cloudsplaining ships with 22 privesc methods that map to the 2018 Rhino Security Labs catalog. Of those 22 patterns, 20 fired on this bench - the two uncaught are privesc9 (AttachRolePolicy) and privesc12 (PutRolePolicy). The Cloudsplaining JSON output marks both policies as not exploitable, probably because the policy documents have resource constraints that Cloudsplaining considers limiting (this is a feature, not a bug, but worth knowing). The other 10 Bishop Fox misses (BF-22 through BF-31: 3-hop AssumeRole chain, CodeBuild, CFN UpdateStack, EC2 Instance Connect, SageMaker variants, SSM:SendCommand, SSM:StartSession) are post-2018 patterns that fall outside Cloudsplaining’s catalog scope - not coverage failures, scope mismatches.
Beyond this matrix: Cloudsplaining covers five categories. PrivilegeEscalation is one. The others (DataExfiltration, ResourceExposure, CredentialsExposure, InfrastructureModification) are not measured here. If you care about policy hygiene more broadly, Cloudsplaining is well-tuned for that use case.
Catalog age: Cloudsplaining’s privesc methods were last meaningfully expanded around 2020. The 2024-2026 patterns (Tier 2/3) are not in scope. This is consistent across the 4 tools that predate cloud-audit’s recent additions.
PMapper (19/57)
Detected service-role chains to admin (PassRole + EC2/Lambda/CodeBuild/SageMaker/SSM/Glue/CloudFormation/DataPipeline) plus its trademark feature: AssumeRole chain detection through trust policy graph traversal. PMapper found Bishop Fox’s 3-hop chain (BF-22) that cloud-audit missed by design.
What it skipped: Anything that is not a path-to-admin. Resource Policy Abuse (CT-1, CT-2) is not “I become admin,” it is “I invoke the privileged Lambda from outside.” MFA bypass alone is not escalation, it is precondition. SSM:GetParameter as credential access does not directly grant admin, it leaks secrets. PMapper’s design is “graph of who can become admin,” and it is consistent with that scope.
Critical context: PMapper is unmaintained. Last release v1.1.5 in January 2022. Open issues #130/131/140 confirm Python 3.10+ is broken; they have been open for over four years with no fix. To run it on a modern system, install Python 3.9 alongside your default Python and create a dedicated venv. For practical 2026 use this is friction, but the tool still works and its lateral detection is conceptually solid. For a different take on IAM privesc analysis without PMapper’s friction, see Debugging AWS IAM and Privilege Escalation Using Multi-Model AI - using LLM consensus instead of static graphs.
CloudFox (4/57)
Detected wildcard trust, cross-account root, and two trusts to admin roles. The four “Y” entries come from CloudFox’s role-trusts enumeration which flags IsAdmin?: YES for roles holding admin policies, and surfaces wildcard * and external :root principals as visible columns.
This is not privilege escalation detection as the other tools do it. CloudFox does not match a principal’s permissions against an escalation catalog and report a method. It enumerates AWS resources (Lambda, EC2, secrets, role trusts, instance profiles, etc.) and presents them in tables a pentester reads to find paths manually. The pmapper subcommand is meant to enrich this with PMapper graph data - on my system it could not find PMapper data even after I generated it (the cached path differs between the two tools’ default locations).
Comparing CloudFox 4/57 to cloud-audit 53/57 is a category mismatch. Including it in this matrix only makes sense because it gets recommended alongside privesc tools in some lists. The honest read is “use it for offensive recon; do not expect it to scan your account for chain detection.”
Caveats
1. Test bench bias. 25 of 57 paths are from cloud-audit’s catalog. Cloud-audit was designed to detect them. The structural advantage cannot be removed by adding caveats - it is built into the bench. The defense is that all 25 custom paths are documented attack vectors with cited references (HackingTheCloud, Praetorian, CVE-2025-14503, AWS docs, Elastic detection rules). They are not invented for the matrix. Falsifiability commitment: the next iteration of this benchmark will replicate against the canonical 65 pathfinding.cloud paths instead of my 57-path bench. If cloud-audit underperforms there - including on the eight paths I excluded for cost or complexity - I will publish that result with equal prominence.
2. Real-world relevance. Some bench paths are more important than others in practice. WildcardTrust and CrossAccountRoot ship with real CVEs (CVE-2025-14503 from December 2025 against Harmonix on AWS EKS). Trust policy misconfigurations are common in the wild - see The GitHub Actions OIDC Mistake That Backdoors Your AWS for one I found in a live audit. SSM compute hijack happens in real incidents. Resource Policy Abuse on Lambda is documented but rarely exploited in the wild compared to PassRole patterns. A more useful version of this matrix would weight paths by observed incident frequency - that data is harder to come by.
3. Tool scope. Privilege escalation is one dimension. Picking a tool only on this matrix is wrong. Prowler beats everyone on compliance breadth. Cloudsplaining covers 4 other categories (data exfiltration, resource exposure, credentials exposure, infrastructure modification) not measured here. CloudFox is offensive recon. Most production teams should run multiple tools.
4. Detection quality is not equal. “Y” entries are not interchangeable. Cloud-audit assigns a method name and severity to each finding. Prowler reports the offending policy without saying who has it attached. Cloudsplaining lists method + policy + attached-to summary. PMapper outputs human-readable text describing the path. CloudFox enumerates trusts. Same column, different evidence.
5. PMapper is functionally dead. January 2022 last release, broken Python 3.10+, four-year-old issues unresolved. The reason it is in this matrix at all is that it is still cited as the OSS reference for chain detection. Production use today requires a Python 3.9 venv hack. If NCC Group revives the project, this caveat goes away. As of April 2026, it has not.
6. Datadog’s pathfinding.cloud has 65 paths, this bench has 57. I did not replicate eight paths that require additional resource provisioning (Lambda + DynamoDB triggers, IAM Identity Center, Glue Sessions with attached connections). They were excluded for cost and complexity, not because they do not matter. Datadog’s library remains the canonical reference.
7. Heuristic matching has noise. I built the coverage matrix by string-matching resource names and method names against each tool’s output. For Prowler (which reports policies, not principals) the mapping required navigating from policy name back to attached principal. For CloudFox the initial heuristic gave a false-positive 36/57 because every enumerated role appeared in the output - the corrected number is 4/57. Other tools may have similar second-order corrections I did not catch. Manual review of the matrix is recommended before drawing strong conclusions.
Back to the 42% claim
Datadog’s exact claim: “Of the 65 paths currently in the pathfinding.cloud library, 27 of them, or 42%, are not detected by any of the open source tools we evaluated.” Datadog Security Labs (Seth Art) does not name every evaluated tool in the article, but the pathfinding.cloud README cross-references PMapper, Cloudsplaining, and Prowler under “Detection Tool Coverage”. The article itself also references PMapper (Erik Steringer / NCC Group) and IAM Vulnerable (Bishop Fox, used as the 31-path test bench in earlier 2021 research, not as a detection tool). cloud-audit was not part of their evaluation - the Tier 1/2/3 patterns landed in v2.0 and v2.1.0, both after their paper went out.
If I run the same exercise on my 57-path bench using the four non-cloud-audit scanners (Prowler, Cloudsplaining, PMapper, CloudFox), the result is 15 of 57 (26%) undetected - all of them custom Tier 1/2/3 patterns. The classic Bishop Fox paths (BF-1 through BF-32) are caught by at least one of the four. The 42% does not reproduce here because my path set partially overlaps Datadog’s, not because the underlying claim is wrong. My set adds CloudFox (offensive recon) where Datadog’s reference set leans on IAM Vulnerable (a vulnerable test lab) - different role, same column.
Add cloud-audit as the fifth scanner and the undetected count drops to zero on my bench. Not because cloud-audit is a silver bullet - because 25 of the 57 paths are exactly the patterns cloud-audit’s catalog was built to detect. That’s the structural bias I disclosed up front.
The honest read of Datadog’s 42% in 2026:
- The number was accurate for the open-source tools they evaluated against their 65 paths in late 2025.
- A new entrant (cloud-audit) closes part of the gap for current attack patterns, but no single tool catches everything.
- Multi-tool setups are still the practical answer. On this 57-path bench, cloud-audit + Prowler covers 56/57; adding PMapper or CloudFox closes the last gap (BF-22, the 3-hop AssumeRole chain).
The obvious follow-up benchmark would be replicating against the canonical 65 pathfinding.cloud paths instead of my 57-path bench. That’s on my list.
What this means in practice
The matrix says cloud-audit detects the most paths in this specific test against this specific bench. That is not the same as saying cloud-audit is the best AWS security tool. The honest takeaways:
- For privilege escalation, especially modern patterns (2024-2026): cloud-audit covers the most ground. PMapper’s lateral detection is conceptually equivalent for chains it sees, but its catalog stops in 2022.
- For compliance evidence and breadth: Prowler is in a different league. 572 checks, multi-framework, GuardDuty integration. Privesc is one footnote among many.
- For policy hygiene including data exfiltration and resource exposure: Cloudsplaining covers five categories. The privesc score in this matrix understates its value if you care about the other four.
- For offensive reconnaissance against an AWS account: CloudFox. Do not run it for chain detection.
- For lateral movement specifically, in 2026: cloud-audit if you can run it. PMapper if you have already spun up a Python 3.9 venv and prefer its graph queries (
who can Xstyle).
Most production teams should be running more than one. The numbers above are not a ranking - they are a coverage map for one specific dimension. For a broader audit framework that combines multiple tools and threat models, see AWS Security Audit: 17 Issues in Every Account or my AWS Security Audit service.
Reproduction
Test bench setup, AWS commands, tool installation steps, and output normalization scripts are published at the cloud-audit repository on GitHub. The benchmark is reproducible in a fresh AWS sandbox at near-zero cost: the 57 paths are primarily IAM resources (free), plus a handful of stub compute resources for paths that require them (BF-25 EC2 Instance Connect, BF-26 to 29 SageMaker notebooks, BF-30 to 31 SSM-managed instances, CT-3 to 7 EC2/ECS, CT-16/CT-20 AppRunner). Run on minimum sizes (t3.nano, no-op Lambda, smallest SageMaker notebook) and terraform destroy after each test - expect under $1 total if you keep the bench up for a single afternoon.
Closing note
I wrote and published cloud-audit. I wrote this benchmark. The bias is structural and disclosed. If you pick a different tool after reading this matrix, that is the right outcome - the goal was not to sell mine, it was to publish numbers Datadog’s pathfinding.cloud paper omitted. If your threat model is “find every documented IAM privilege escalation path in our AWS account, including 2024-2026 patterns,” cloud-audit is currently the best fit on this bench. If your threat model is anything broader, the answer is different.
The matrix and raw tool outputs will be republished if any of the OSS tools updates its catalog or detection logic - particularly if NCC Group revives PMapper.
Sources and references
- Datadog Security Labs: Introducing Pathfinding.cloud (December 17, 2025)
- DataDog/pathfinding.cloud GitHub repository
- Bishop Fox iam-vulnerable Terraform module
- PMapper (NCC Group) GitHub - issues #130, #131, #140 for Python 3.10+ compatibility
- CloudFox documentation
- Cloudsplaining documentation
- Prowler v5 documentation
- Praetorian: AWS IAM Assume Role Vulnerabilities Found in Many Top Vendors (2022)
- HackingTheCloud: AWS IAM Privilege Escalation Techniques
- Rich Infante: Privilege Escalation in EC2 using Session Manager (August 2024)
- Elastic Security: AWS STS Role Chaining detection rule
- AWS Security Bulletin AWS-2025-031: Harmonix wildcard trust (CVE-2025-14503)
- Bishop Fox: Investigating Privilege Escalation Methods in AWS